Return to Dragon Pass with The Red Cow Campaign by Ian Cooper, Jeff Richard, and Greg Stafford
 |
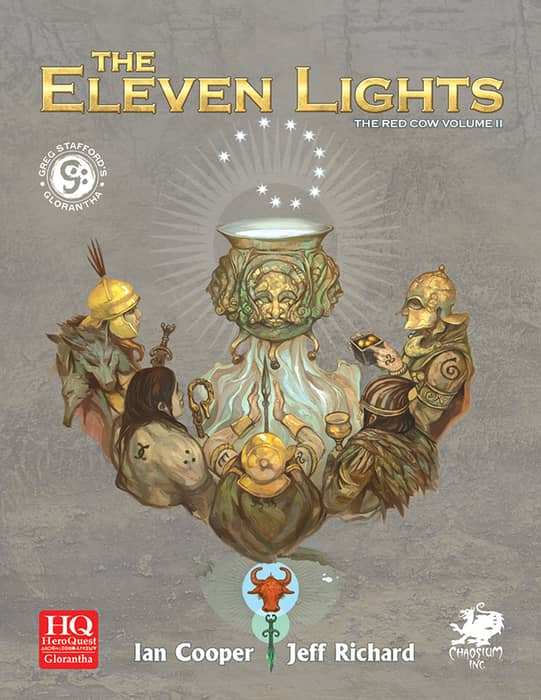 |
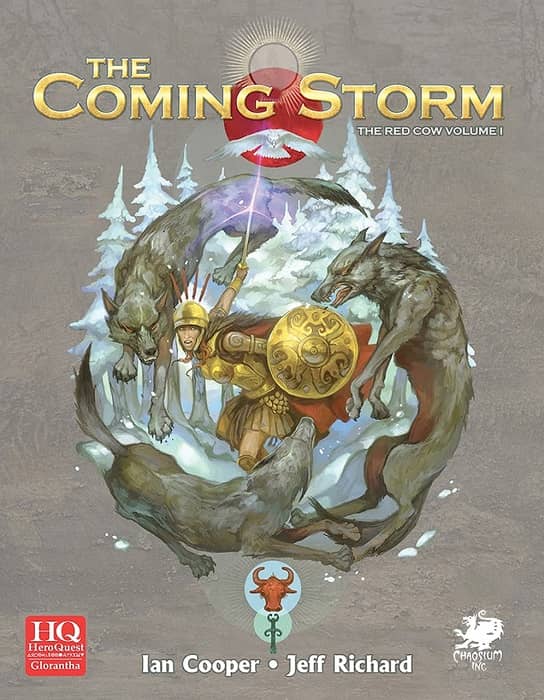
The Coming Storm (March 2016) and The Eleven Lights (April 2018), published by Chaosium
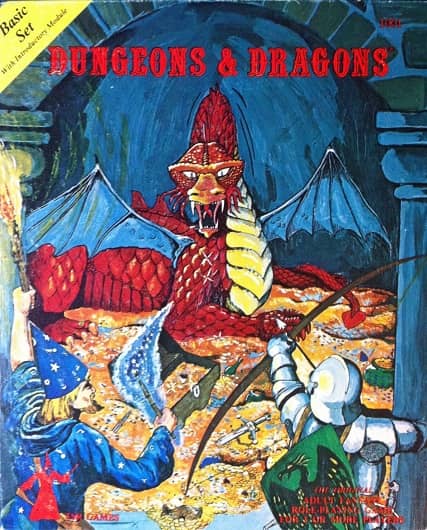
We live in a Golden Age of board gaming, and if you’re in the market for a fantasy game, you literally have thousands to choose from. Mind you, that wasn’t the case 40 years ago. In fact, if you were looking for a serious fantasy-based pastime in those days, there were literally only a few games in town: SPI’s War of the Ring (1977), TSR’s Divine Right (1979), and Chaosium’s Dragon Pass (1981).
In terms of gaming history, there’s little question that by far the most important of those was Dragon Pass. It was originally developed in 1975 by Greg Stafford, and published under the name White Bear and Red Moon. Stafford decided to form a company to produce and market it; inspired by the nearby Oakland Coliseum, he called his new enterprise ‘Chaosium.’ Stafford sold White Bear and Red Moon, and its sequel Nomad Gods, in ziplock bags out of his house in Oakland. Chaosium grew rapidly, and in less than ten years was one of the most important publishers in the industry. If it weren’t for the early success of White Bear and Red Moon and its sequels, we wouldn’t have RuneQuest, Thieves World, and Call of Cthulhu, just to name a few.
The setting for White Bear and Red Moon, a Bronze Age world rich with human and nonhuman gods, cults, clans and mythology, was Glorantha. Today Glorantha is one of the most important settings in modern fantasy, home of numerous role playing campaigns, board games, novels and stories, and even a popular computer game, King of Dragon Pass. There are many reasons for its popularity and longevity, of course, but personally I believe Dragon Pass — the game that introduced Glorantha to the world — deserves much of the credit. If you’ve spent hours staring at the colorful map of Glorantha, moving your outnumbered clans across the rugged terrain of Sartar, through the Skull Ruins and towards a desperate battle in Snakepipe Hollow, the chance to visit those iconic settings in a role playing environment is just too irresistible.
A few years ago Chaosium released an epic two-part campaign set in Glorantha that explores much of the history and rising tensions that eventually exploded into the Hero Wars: The Coming Storm and The Eleven Lights, which together comprise the Red Cow Campaign. I recently purchased both books, and have really been enjoying this chance to revisit the colorful and dynamic setting where I spent so much time in my youth.


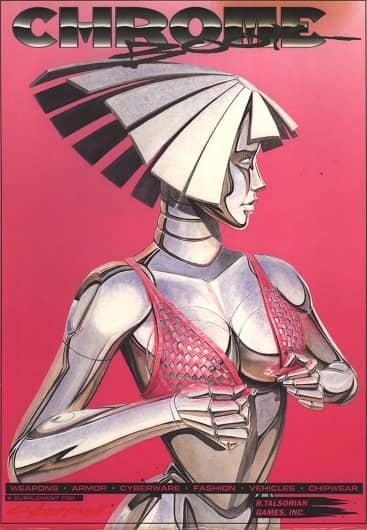
 Degenesis, SixMoreVodka’s post-apocalyptic, Europe-and-North Africa-centered tabletop RPG, released its first rules expansion last month. Called Artifacts and featuring the new Degenesis black-and-gold look, it’s the first gaming supplement I’ve ever owned with gilt-edged pages.
Degenesis, SixMoreVodka’s post-apocalyptic, Europe-and-North Africa-centered tabletop RPG, released its first rules expansion last month. Called Artifacts and featuring the new Degenesis black-and-gold look, it’s the first gaming supplement I’ve ever owned with gilt-edged pages.